Ransomware Incident: Lessons and Strategies for Protection
On December 2nd, 2022, Rackspace encountered a significant security incident that was subsequently identified as a ransomware attack, impacting a substantial user base. Rackspace, known as a leading public cloud computing company and early cloud solutions provider, experienced a breach that prompts an essential discussion on both the incident itself and the critical measures organizations can take to shield themselves from future ransomware threats, whether targeting their internal systems or technology vendors.
Rackspace Ransomware Incident Overview
The Rackspace ransomware incident made headlines due to its scale, affecting tens of thousands of users. Rackspace responded swiftly by migrating a substantial number of users to Microsoft Office 365, aiming to mitigate the impact of the attack. However, the exact entry point of this ransomware attack remains undisclosed. Still, circumstantial evidence strongly suggests that it could have exploited an unpatched vulnerability within Microsoft Exchange, a favored target among cyber attackers in 2022.
Understanding Ransomware Attacks
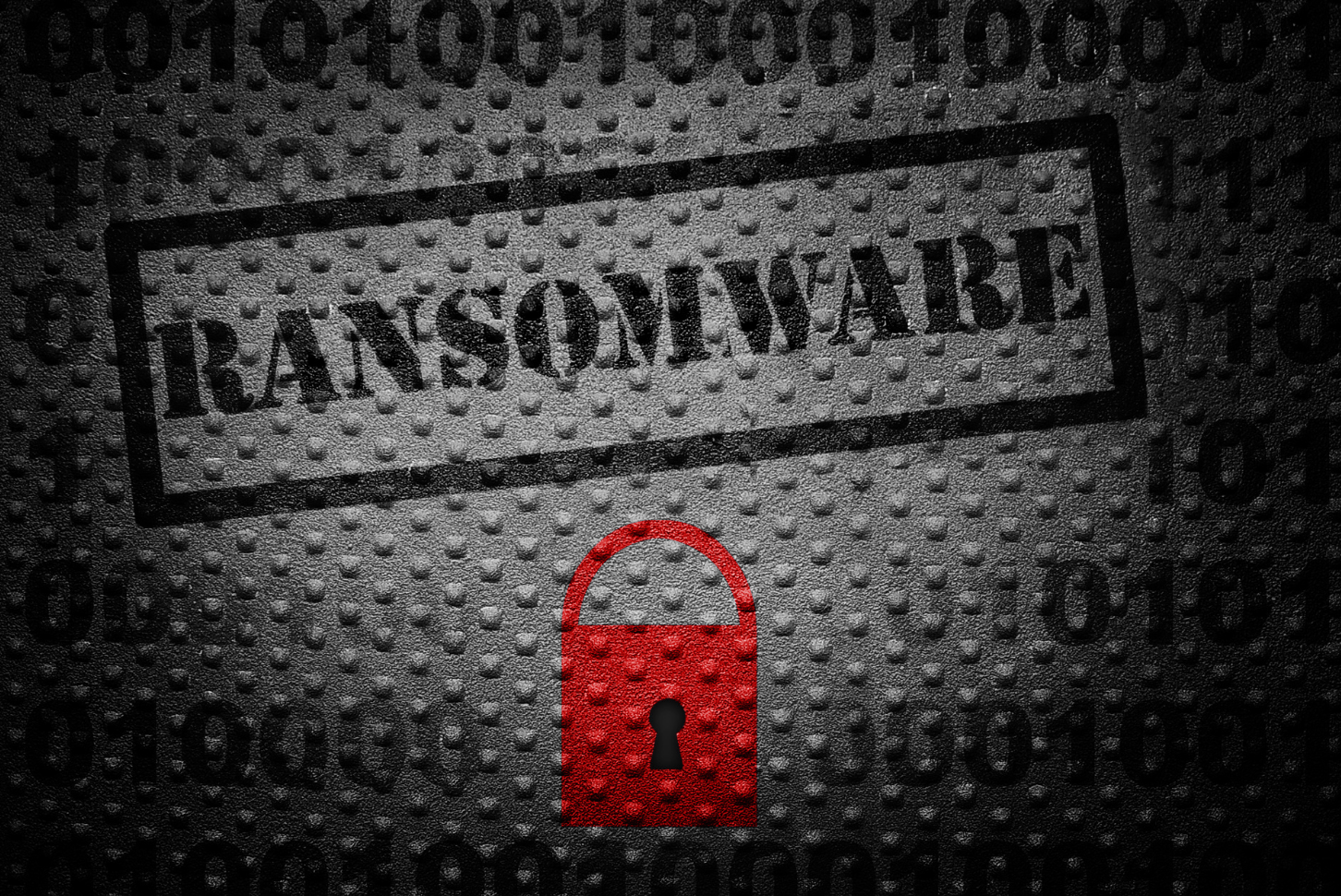
Understanding the mechanics of ransomware attacks is crucial in protecting your organization. A ransomware attack typically combines encryption software with the actions of hackers. This malicious software encrypts critical data, rendering it inaccessible until a decryption key is provided, often in exchange for a ransom payment. The initial installation of ransomware can occur through various means following the compromise of your network. Additionally, a disturbing trend in recent years involves attackers exfiltrating data during the attack, storing it in cloud storage, and then demanding payment not only for the decryption key but also to prevent the public sale or disclosure of stolen data.
Protecting Your Organization from Ransomware Attacks
Safeguarding your organization against ransomware attacks is a complex undertaking, as these attacks often occur after an initial compromise, which can result from a variety of vulnerabilities. Common entry points include human errors and the absence of multi-factor authentication (MFA) or unpatched security weaknesses that hackers can exploit. One effective strategy is to adhere to the Center for Information Security (CIS) 18 critical security controls, which address the most prevalent risk factors leading to compromises. These controls are regularly updated to reflect emerging threats and are designed to mitigate 98% of risks. Additionally, investing in cyberattack insurance is essential, as no security measures can guarantee complete protection.
Protecting Your Organization from Vendor Security Incidents
Furthermore, safeguarding your organization against security incidents involving technology vendors requires a proactive approach. Two crucial ISO standards are recommended:
- ISO 27001 Section 15 – Supplier Relationships: This standard empowers organizations to gain control and awareness of their suppliers and vendors, enabling them to assess potential risks before an incident occurs.
- ISO 22301 Security and Resilience – Business Continuity Management Systems: This standard helps organizations develop a comprehensive plan for various incident scenarios, which should be regularly tested to enhance preparedness.
While the Rackspace hack serves as a cautionary tale, it offers valuable lessons that organizations can apply to reduce the risk of falling victim to similar attacks. By implementing robust security controls, procuring cyberattack insurance, and adopting ISO standards for vendor relationships and business continuity, organizations can bolster their defenses against ransomware attacks in an evolving threat landscape. The incident underscores the importance of proactive measures in safeguarding sensitive data and ensuring uninterrupted business operations.
If you have been a victim of a ransomware attack or would like to learn more about preventing them, please contact us. We would love to help!